Why Choose Walden?
Program Details
Curriculum
Completion Requirements
- 45 quarter credits
- Core courses (45 qtr. cr.)
View the COMPLETE CURRICULUM PLAN.
Admission Requirements
To be considered for this master’s program, you must have a technical bachelor’s degree or at least one year of relevant professional experience in information technology and meet the general admission requirements. All graduate IT programs in the College of Management and Human Potential require the submission of a résumé. Proficiency in at least one modern programming language is highly recommended but not required. All applicants must submit a completed online application and transcripts. More information for international applicants.
Questions about the courses you will take?
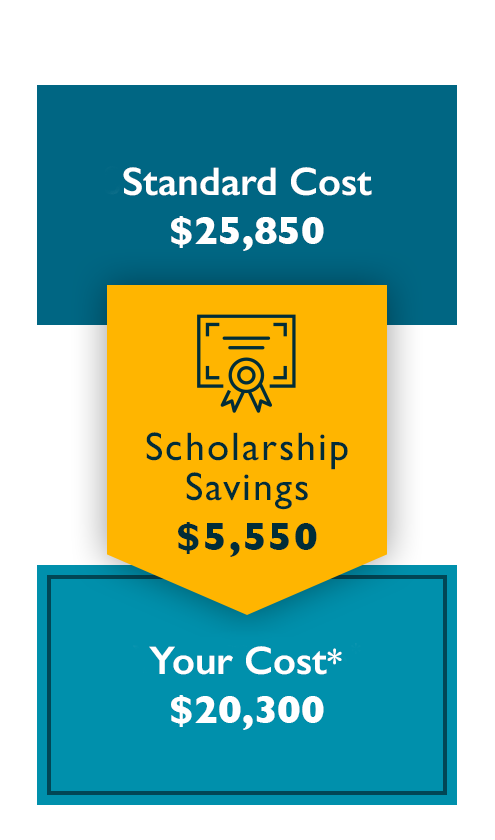
| Curriculum Component | Requirements | Cost | Amount |
|---|---|---|---|
| Tuition | 45 quarter credit hours | $555 per quarter hour | $24,975 |
| Program Fee | Per quarter | $175 | $875 |
| $25,850** | |||
| BELIEVE & ACHIEVE SCHOLARSHIP YOUR TUITION | -$5,550 $20,300* | ||
*Represents minimum time to completion and Believe & Achieve Scholarship. Your actual total program time and costs may vary. Believe & Achieve Scholarship savings based on current tuition. See Scholarship Details for more information.
**Tuition reflects the minimum time to completion. Time to completion varies by student, depending on individual progress and credits transferred, if applicable. Tuition and time to complete may be reduced if transfer credits are accepted, or if you receive grants, scholarships, or other tuition reductions. Walden may accept up to 20 transfer credits. For a personalized estimate of the number of your transfer credits that Walden would accept, call an Enrollment Specialist at 844-529-2438.
Tuition and fees are subject to change. Books and materials are not included and may cost up to an additional $1,000 and $1,400.
Program Outcomes
Build Your Expertise in Cyber Operations
In our online master’s in cybersecurity program, you’ll develop a strong foundation in information systems and cyberattack detection and remediation. Gain hands-on experience with industry-leading tools and their practical application in various settings and threat scenarios. Explore groundbreaking advances in cyber forensics, cybercrime prevention, and secure coding as you build the confidence to lead critical information security initiatives and cross-functional teams.
Career Outlook
Business and government organizations need highly trained security engineers to protect their networks and sensitive data from cyberattackers. According to the Bureau of Labor Statistics (BLS), jobs for information security analysts are expected to grow 35% by 2031—much faster than average.1
That’s good news for driven IT professionals like you. A cybersecurity master’s degree can prepare you to meet the demand for skilled talent and lead large-scale information security initiatives.
An MS in Cybersecurity degree can prepare you to pursue career options such as:2
- Information security engineer
- Information systems/technology security analyst
- Information systems/technology manager or supervisor
An MS in Cybersecurity degree can prepare you to work in settings such as:
- Government
- Financial institutions
- Education
- Nonprofit organizations
Career options may require additional experience, training, or other factors beyond the successful completion of this degree program.
Learning Outcomes
Graduates of Walden’s cybersecurity master’s online program will be prepared to:
- Evaluate emerging technical developments that apply to cybersecurity.
- Evaluate the role of cybersecurity elements within the context of the modern workplace.
- Examine cryptography elements for practical application in both commercial and non-commercial settings.
- Critique cybersecurity strategies that can be deployed to prevent cybercrime.
- Examine computer forensics elements for their practical usage in both commercial and non-commercial organizations.
- Evaluate management processes that can be deployed to prevent or limit potential cyber-attacks in the workplace.
1Source: Bureau of Labor Statistics, Occupational Outlook Handbook, Information Security Analysts, SOC code 15-1212.
2Source: O*Net Online. Cyber Security Jobs (SOC Codes: information security engineer 15-1299-05, information systems/technology security analyst 15-1212, information systems/technology manager or supervisor 11-3021.)